When I have designed wargames around a NATO-Russia conflict, I often left out cyberattacks for a simple reason: it was just too complicated. Too many unknowns make an accurate simulation impossible.
The number of targets, scale of the attack, damage done, how the attack could be carried out and its ramifications were beyond calculation for a mere simulation on the scale I was running using just consumer-based computer technology.
Honestly, nuclear war seemed easier to think about, and that says a lot.
But that should give us pause. Our world is basically a giant computer now, with cloud-based networks controlling virtually every aspect of our lives, from sewage and water treatment plants, to our electrical grid, to our smart homes, and on and on we go. While we like to think of those systems as secure, we have never been part of a conflict where those systems were targeted en masse with the goal of rendering them disabled or destroyed.
In fact, many policymakers seem to get the willies when you ask them about cyberwarfare even in the most basic of scenarios, but especially now when we talk about Russia launching a cyberattack to avenge the recent sanctions. When I asked a former Trump National Security Council member what a cyberattack on the United States might look like by Russia, the response was essentially: “A cyberattack is like throwing a grenade but not knowing when, if or upon whom it will explode. It might even explode on you. Pray no nation with a large cyber capacity goes to war deploying such weapons — we don’t really know where it leads.”
My contact called me back to add that:
Using a cyberweapon in a massive attack is like firing a spread of nuclear weapons, except you can never be sure if you hit the target until you see systems and users get impacted, or you create billions of dollars in collateral damage you did not intend to create. The oops factor is too high for these weapons to be called precision. They are weapons of mass chaos.
The “oops” factor is the key. Just because Russia targets a specific sector of our economy or the military doesn’t mean the malware or virus used to carry out the attack won’t move into the greater computer universe, as those same style computers and servers can power civilian applications as well, and malware loves to spread.
In fact, that is the danger of any sort of cyberwar between the US and Russia or any nation; once you let the malware out into the wild, you never know where it could end up.
A simple example of a Russian cyberattack spells out how this could happen: let’s say Moscow wanted to attack a US bank, Wells Fargo, for example. How would they do it?
One way could be to try to find employees who work for the company and send them malware via email spear-phishing attacks — emails that look as if they could be from a friend or family member that get them to click on a hyperlink. That hyperlink, when activated, can inject malware onto a phone or infect a computer. The Russians would then hope the computer or smartphone is connected to the Wells Fargo network, where it can jump onto other computers. That’s all it takes.
Here’s where things get a little complex. US cybersecurity experts I have spoken to think Russia has surely compromised at least one or two US banks and has malware and viruses in banking networks ready to go, just lying in wait. So what would those viruses do when activated? Most likely, they will deprive consumers of their cash by infecting the network or computers and servers responsible for basic banking operations. Imagine Wall Street waking up one morning and Wells Fargo or Bank of America telling the world millions of Americans can’t access their cash. Stock markets would crash, there would be runs on banks and mass mayhem.
That’s not all. That malware then gets out into the wild, with anonymous hackers getting the source code and attacking two other US banks just for spite. That’s the great challenge of cyberwar: once you fire off your weapons, that same code can be reused and repackaged to attack others.
Of course, this would be just hitting one bank with follow-on attacks coming from cyber opportunists. Would Russia really stop there? Perhaps, as Moscow might want to display its powers in a simple and straightforward manner, unleashing chaos and moving on.
But let’s say Russia wants to get even moderately fancy and have more deniability. It could easily infect Windows-based PCs around the world that have not done regular security updates in mass and launch what is called a “denial of service attack” attack. A DoS attacks a computer network or website with millions of fake requests for access. Attribution is hard to achieve in that so many millions of connections would hit the server all at once and would be launched from unsuspecting computers all over the world that are infected with the malware. Again, containing the attack is the problem, as the code used in the attack could be reused by other hackers in the future, spreading the problem.
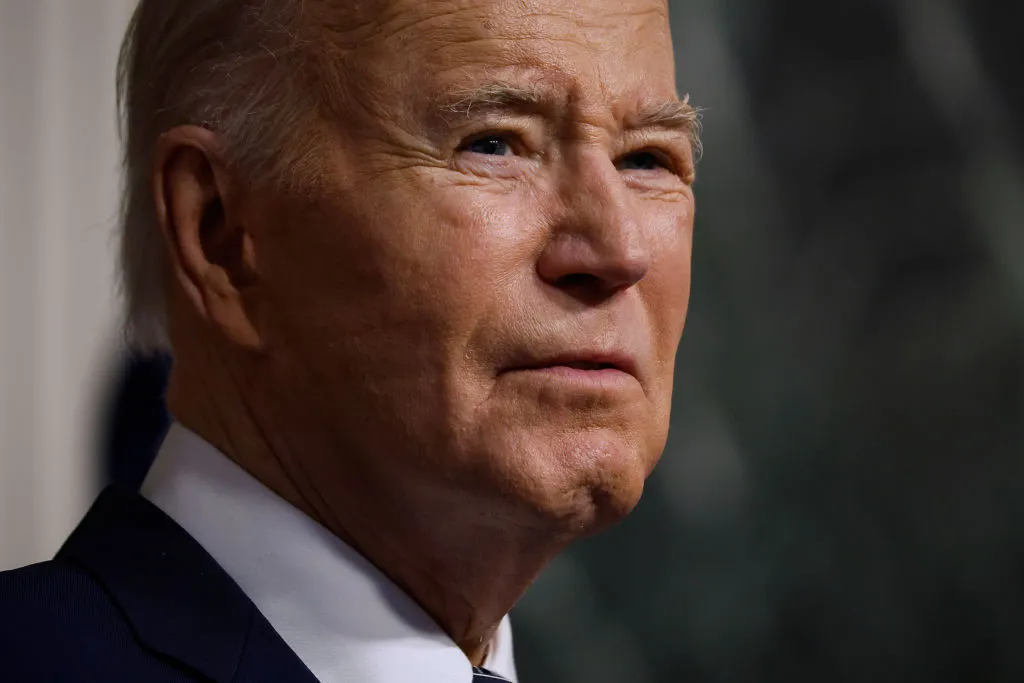
Then there is the problem of how to respond. What would the United States do if either of these scenarios occurred? Also, does a cyberattack constitute an Article 5 situation and bring in the NATO alliance?
These are the questions the White House is presumably trying to answer as they suspect Russia could strike soon. My guess is that US cyber command surely has its hooks into critical components of Russia’s economy and military and is ready to hit back in a similar way, as they likely have malware stashed deep in those systems. But at what point does such a cyberwar cross into the physical world? It seems that someday — perhaps not now between Russia and the US — but soon, two or more nations are destined to find out.